A Practical Cloud Governance Framework for AWS, Azure, and GCP
A cloud governance framework is the set of policies, procedures, and technical controls that dictate how your organization manages, secures, and operates in the cloud. It’s a technical blueprint designed to enable innovation while managing cost, security, and compliance.
This guide provides an actionable blueprint for building that framework, relevant for any organization from a startup to a large enterprise operating in 2026.
Why Your Cloud Environment Needs a Governance Blueprint

Operating in the cloud without governance is like building a city without zoning laws or building codes. The initial freedom for developers to deploy services and provision resources leads to rapid, uncontrolled growth. This quickly descends into chaos.
The results are predictable: budgets spiral, often exceeding forecasts by 30% or more. Security vulnerabilities emerge in unexpected places. Compliance becomes a reactive, high-stress exercise. The environment becomes a tangled mesh of inconsistent infrastructure, duplicated effort, and untraceable costs.
Moving from Restrictive Rules to Automated Guardrails
A modern cloud governance framework is not a restrictive rulebook that slows down engineering. Its objective is to establish automated guardrails that enable teams to innovate safely within well-defined boundaries.
A well-designed framework turns governance from a bottleneck into a business enabler. It provides the structure to manage risk and control costs, freeing up engineering teams to focus on building value, not fighting infrastructure fires.
This structured approach is a technical and business necessity. The market for cloud governance tools, a core component of any framework, is valued at USD 1.5 billion in 2025 and is projected to grow at an 8% CAGR. This growth is a direct response to the broader cloud market’s expansion, expected to grow from $905.33 billion in 2026 to $2,904.52 billion by 2034.
With large enterprises now directing 62.3% of hybrid cloud spending, governance is the essential stabilizing force in complex, multi-cloud architectures.
The Urban Planning Analogy: A Technical View
The city planning analogy provides a useful technical model. Your governance framework functions as the urban planning commission for your digital infrastructure. It doesn’t lay every brick but defines the critical rules for sustainable growth.
- Zoning Laws (Policy Enforcement): Defines where specific resources can be provisioned (e.g.,
prod-us-east-1vs.dev-eu-west-2) and what services they can connect with via network policies. - Building Codes (Security Standards): Mandates non-negotiable security standards for every deployment, such as requiring encryption-at-rest for all storage volumes and enforcing least-privilege IAM roles.
- Infrastructure Permits (Cost Control): Requires budget approval and cost-center tagging before provisioning large-scale resources, preventing uncontrolled spend.
- Public Utilities (Operational Consistency): Ensures shared services like networking, observability pipelines, and identity management are consistent, reliable, and available to all business units.
Framed this way, governance is a strategic tool that ensures every component of your cloud environment is built securely, on-budget, and in the correct operational context. This guide provides the technical details to construct that blueprint.
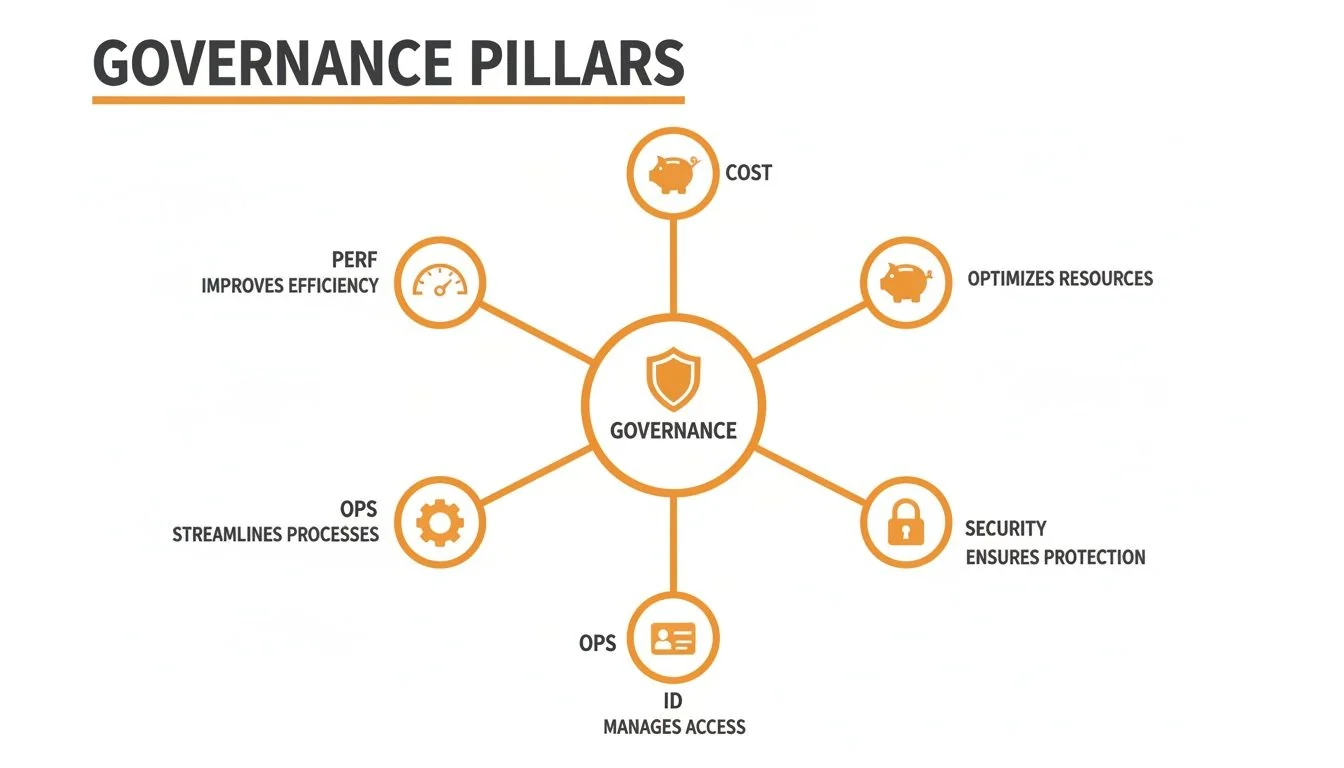
The Five Pillars of a Cloud Governance Framework
A robust cloud governance framework is a system of interconnected controls built on five pillars. Each addresses a specific domain of risk and operational efficiency. When implemented together, they form a stable foundation for scalable cloud operations.
These pillars are the support columns of your cloud architecture. A weakness in one compromises the entire structure. A balanced implementation is critical for long-term stability and performance.
1. Cost Management and FinOps
This is the initial driver for many governance initiatives, typically following a significant and unexpected cloud bill. Effective governance moves beyond reactive cost analysis to a proactive culture of financial operations (FinOps), where engineers are accountable for the cost of the resources they provision.
A primary source of waste is “zombie” infrastructure: unattached EBS volumes, idle VMs, or deprecated test environments still incurring charges. A direct control is to implement automated shutdown scripts that scan for non-production tagged resources and terminate them outside of business hours, often reducing dev/test costs by over 50%.
Mandatory, enforced tagging is non-negotiable.
- Policy Enforcement: Utilize native services like AWS Service Control Policies (SCPs) or Azure Policy to programmatically deny the creation of major resources (e.g., EC2 instances, RDS databases) if they lack essential tags like
owner,project, andcost-center. - Automation: This is not an honor system. The policy blocks the API call, preventing the launch of untagged resources and enforcing compliance at the point of creation. This ensures 100% of cloud spend is attributable.
2. Security and Compliance
The security pillar establishes non-negotiable guardrails to protect data and applications. The modern approach is preventative, using policy-as-code to make it impossible to deploy insecure configurations.
Governance isn’t about telling developers “no.” It’s about building a system where the secure way is the only way. Preventative controls are how you scale security without a linear increase in security personnel.
A classic example is preventing publicly accessible S3 buckets or Azure Blob Storage containers. Instead of relying on post-deployment scanning, you prevent the action entirely.
- In AWS: An SCP can be configured to deny the
s3:PutBucketPublicAccessBlockAPI call if the parameters would permit public access. The request fails. - In Azure: An Azure Policy definition can be set to “deny” the creation of any storage account where the
allowBlobPublicAccessproperty is true.
These controls operate at the API level, making non-compliant resource creation impossible. The same logic is applied to block unencrypted database provisioning or prevent security group rules that open SSH access to the internet (0.0.0.0/0).
3. Operations Management
This pillar ensures consistency, reliability, and operational hygiene. Its primary function is to prevent configuration drift and enforce standardized, repeatable deployments. Without it, environments become a chaotic mix of bespoke configurations that are impossible to manage, patch, or secure at scale.
A cornerstone is mandating the use of Infrastructure as Code (IaC) through approved, version-controlled templates, such as reusable Terraform modules or AWS CloudFormation templates. Governance dictates that all production infrastructure must be provisioned via these modules.
For example, an approved Terraform module for a web application tier automatically includes:
- Configuration to stream logs to a central SIEM.
- Standard agents for performance and security monitoring.
- Required tags for cost allocation, asset inventory, and security posture management.
4. Identity and Access Management
In the cloud, identity is the perimeter. This pillar focuses on enforcing the principle of least privilege—granting every user, role, or service principal the absolute minimum permissions required for its function. Misconfigured IAM permissions are a leading cause of security breaches.
Instead of assigning broad permissions like AdministratorAccess, the framework enforces granular, role-based access control (RBAC). A CI/CD pipeline role, for instance, might have permission to deploy a specific application but be explicitly denied permissions to modify network ACLs or access production data stores.
Modern identity governance also mandates just-in-time (JIT) access. Services like AWS IAM Identity Center or Azure AD Privileged Identity Management (PIM) grant engineers time-bound, audited elevated access for specific operational tasks. The access expires automatically, drastically reducing the attack surface of persistent administrative credentials.
5. Performance and Resilience
This pillar ensures applications meet business requirements for availability and performance. It establishes standards for resource sizing, autoscaling, and disaster recovery.
Governance here prevents common anti-patterns, such as overprovisioning compute resources “just in case.” A key control is to require autoscaling policies for all production workloads. For example, an Azure Policy can audit for Virtual Machine Scale Sets that lack a configured autoscaling rule. This ensures applications can handle traffic spikes and, equally important, scale down to optimize costs. This pillar ensures your cloud is not only secure and cost-effective but also resilient and performant.
Mapping Governance Controls to AWS, Azure, and GCP
A cloud governance framework remains theoretical until its principles are mapped to the specific, native services of the major cloud providers. The objective is constant—cost control, security, and operational stability—but the tooling differs across Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
Understanding which service implements which control is critical for effective execution, especially in multi-cloud environments.
These pillars represent the core domains your governance strategy must integrate. A strong framework ensures that controls in one area, such as cost management, do not adversely affect others, like security or operations.
Governance Controls Mapping Across Major Cloud Platforms
To implement governance, you must translate abstract policies into concrete configurations using native tools. A policy to “prevent budget overruns” becomes a programmatic rule in AWS Budgets or a defined policy in Azure Policy. Here is a mapping of the core governance pillars to services across the three major cloud providers.
| Governance Pillar | AWS Service Example | Azure Service Example | GCP Service Example |
|---|---|---|---|
| Cost Management | AWS Budgets & Cost Explorer | Azure Cost Management and Billing | Cloud Billing Budgets |
| Security & Compliance | AWS Security Hub & AWS Config | Microsoft Defender for Cloud | Security Command Center |
| Identity & Access | AWS IAM & IAM Identity Center | Azure Active Directory (Azure AD) | Cloud IAM |
| Resource Management | AWS Resource Groups & Tag Editor | Azure Resource Groups & Tags | Projects, Folders, & Labels |
| Operations | Amazon CloudWatch & AWS Systems Manager | Azure Monitor & Azure Automation | Cloud Monitoring & Cloud Deployment Manager |
This mapping is about understanding each platform’s architectural philosophy—from AWS’s account-based isolation to Azure’s resource group aggregation—and how it impacts the implementation and enforcement of your governance controls.
For a deeper technical analysis of these platforms, our comprehensive comparison of AWS vs Azure vs GCP details the key architectural differences.
Cost Management and FinOps Tooling
All three providers offer robust toolsets to track, control, and optimize cloud expenditure. A sound governance framework mandates their use to prevent budget overruns.
-
On AWS: AWS Budgets is used to set custom cost and usage thresholds with alerts. For proactive control, AWS Cost Explorer enables deep analysis of spend data, while Service Control Policies (SCPs) can programmatically block the provisioning of expensive or unapproved service types.
-
In Azure: Azure Cost Management and Billing provides a central dashboard. Budgets can be configured to trigger automated actions, such as executing an Automation runbook to shut down a resource group when a cost limit is reached. Azure Policy is also used for cost control by enforcing rules like restricting deployments to specific VM SKUs.
-
With GCP: Cloud Billing Budgets send alerts based on spending targets. GCP’s custom machine types and sustained use discounts are powerful, built-in cost optimization features that a governance strategy must leverage.
Security and Compliance Controls
Modern cloud governance requires a centralized view of security posture. Each provider offers a flagship service to deliver this.
A mature cloud governance framework doesn’t just react to security alerts; it uses native cloud services to provide a single, unified view of compliance. This shifts security from a siloed activity to a shared responsibility, visible from engineering to the C-suite.
Here’s a comparison:
-
AWS: AWS Security Hub acts as a central aggregator, ingesting findings from services like Amazon GuardDuty, AWS Config, and AWS Inspector. It provides continuous compliance checks against benchmarks like CIS, generating a compliance score and prioritized findings.
-
Azure: Microsoft Defender for Cloud integrates Cloud Security Posture Management (CSPM) and Cloud Workload Protection (CWPP). It generates a “Secure Score” based on industry standards like NIST and ISO 27001 and provides actionable recommendations for hardening the environment.
-
GCP: Google Security Command Center provides a unified dashboard for managing vulnerabilities, misconfigurations, and threats. It integrates with other Google Cloud security tools to provide a comprehensive risk management platform across projects.
Identity and Access Management
Controlling authentication and authorization is foundational to governance. While all clouds use the term “IAM,” their underlying models and hierarchies differ significantly.
-
AWS: AWS IAM is used to manage users, groups, roles, and permission policies. At scale, AWS Organizations is essential for managing multiple accounts, while AWS IAM Identity Center (formerly AWS SSO) provides federated access management across all of them.
-
Azure: Azure Active Directory (Azure AD) is the core identity service. It is based on a user-centric model familiar to enterprises, simplifying access management for both cloud and on-premises resources.
-
GCP: Google Cloud IAM uses a resource-centric model. Permissions are bound directly to resources within a strict project-and-folder hierarchy, offering granular control that requires a different mental model than AWS or Azure.
Structuring Your Cloud Governance Team

A cloud governance framework without clear ownership is ineffective. The structure of the team is as critical as the policies it creates. The optimal structure depends on the organization’s size, culture, and cloud maturity. The goal is to define clear ownership and build a culture of accountability.
Defining Key Governance Roles
Effective governance requires assigning specific responsibilities. While titles may vary, the core functions are constant. These roles provide the human intelligence that designs, implements, and iterates on automated controls.
The three essential roles for a modern governance team are:
- Cloud Custodian: The hands-on technical expert who translates policy into code. This role implements IAM roles, configures security services, and builds the automation that enforces governance rules. They codify the rulebook.
- FinOps Analyst: This role is focused on financial accountability. They monitor cloud spend, identify optimization opportunities, and work with engineering teams to implement cost-saving measures. They ensure financial efficiency.
- Cloud Security Architect: This role designs the security controls integrated into the framework. They are responsible for ensuring all deployments meet internal security standards and external regulatory requirements, from data encryption to network segmentation.
Centralized vs. Federated Governance Models
Once roles are defined, their placement within the organization must be decided. Two primary models have emerged.
A Centralized Model, typically organized around a Cloud Center of Excellence (CCoE), is common in large enterprises. A single, dedicated team creates and enforces all cloud policies across the organization.
The CCoE acts as the air traffic control for the cloud environment. It defines standard architectures, provides shared services, and offers expert guidance to ensure safe and consistent operations.
This model provides strong control over security and cost, which is essential in regulated industries. The primary drawback is the potential to become a bottleneck for agile teams.
Conversely, the Federated Model is a decentralized approach favored by startups and agile organizations. A small central team sets the high-level strategy and non-negotiable guardrails, but individual product teams are empowered to implement and manage controls within their own environments.
This model prioritizes autonomy and velocity, aligning with a DevOps culture. The main risk is policy drift, where inconsistent implementation across teams can create security or compliance gaps. The choice between models is a trade-off between tight central control and team autonomy.
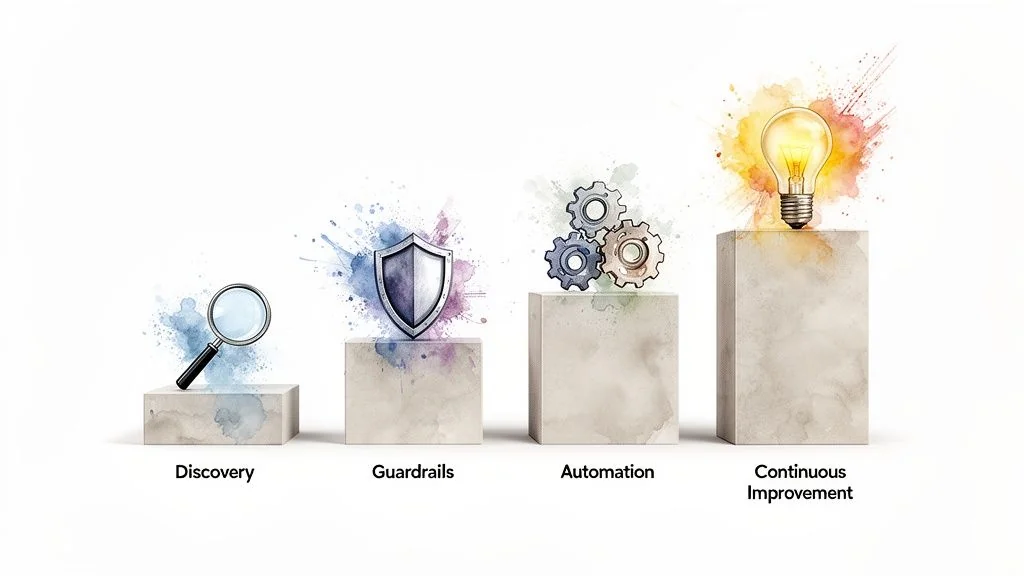
Your Phased Roadmap for Implementing Cloud Governance
Implementing a comprehensive cloud governance framework in a single phase is impractical and leads to analysis paralysis. A pragmatic, phased approach is necessary to achieve tangible results without disrupting business operations.
This roadmap details four sequential stages, each building upon the last, to establish a mature and sustainable governance practice.
The structured approach enabled by these frameworks is driving significant market growth. The cloud governance platform market, valued at USD 2.8 billion in 2024, is projected to reach USD 8.5 billion by 2033, a 15.2% CAGR. For mid-sized companies, these frameworks are crucial for preventing cost overruns that often exceed 30%. For large enterprises, automation can reduce compliance audit times by up to 50%. You can explore the full market analysis on MarketTrendsAnalysis.com for more data.
Phase 1: Discovery and Baseline
You cannot govern what you cannot see. The initial phase is focused on gaining complete visibility into your cloud environment. The objective is to inventory all assets, identify owners, and understand current spending.
Your Action Plan:
- Inventory All Assets: Deploy an asset inventory tool. Use native services like AWS Config or Azure Resource Graph to create a comprehensive catalog of every resource across all accounts and regions.
- Analyze Spending: Use native cost management tools (like AWS Cost Explorer) to create a baseline of cloud expenditure. Identify the top five most expensive services and the highest-spending accounts.
- Identify Critical Risks: Perform an initial security posture scan using a tool like AWS Security Hub or Microsoft Defender for Cloud. Focus on critical misconfigurations like public S3 buckets or unrestricted network access.
The common mistake in this phase is attempting to remediate every finding. The goal is to map the terrain, not perfect it.
Success Metric: You can generate a real-time inventory of all cloud assets and confidently attribute at least 80% of your monthly cloud spend to a specific team or project.
Phase 2: Foundation and Guardrails
With a clear baseline, the next step is to implement foundational controls to mitigate the most significant risks. This phase is about establishing essential security and cost guardrails.
Your Action Plan:
- Mandate Tagging: Use a service like an AWS SCP or Azure Policy to enforce the presence of essential tags (
owner,cost-center,environment) on all new resources. This is a non-negotiable control. - Implement Budget Alerts: Configure automated budget alerts in AWS Budgets or Azure Cost Management for all major projects and accounts.
- Block High-Risk Actions: Deploy preventative policies to block high-risk configurations, such as making storage buckets public, disabling logging, or opening RDP/SSH to the internet (
0.0.0.0/0).
A common pitfall is creating overly restrictive rules that hinder development. Focus initially on high-impact, non-negotiable controls.
Phase 3: Automation and Optimization
With foundational guardrails in place, the focus shifts from defensive measures to proactive automation and optimization. This phase moves from manual remediation to automated enforcement.
Your Action Plan:
- Automate Waste Remediation: Develop scripts (using AWS Lambda or Azure Functions) to automatically identify and terminate waste, such as unattached storage volumes, orphaned snapshots, and idle load balancers.
- Implement Policy as Code: Define governance rules in code using tools like Terraform Sentinel or Open Policy Agent (OPA). Integrate these checks directly into your CI/CD pipelines to prevent non-compliant deployments.
- Automate Rightsizing Recommendations: Use native or third-party tools to analyze performance metrics and automatically generate rightsizing recommendations for overprovisioned VMs and databases.
Success in this phase is measured by a quantifiable reduction in manual operational tasks and wasted cloud spend.
Phase 4: Continuous Improvement and Innovation
In this mature phase, governance is no longer a separate function but is fully embedded into DevOps and FinOps cycles. The objective is to continuously refine policies based on data, empowering teams to innovate safely and efficiently.
Your Action Plan:
- Establish a Governance Cadence: Institute regular (e.g., quarterly) reviews with key stakeholders to assess policy effectiveness, review exceptions, and adapt rules to new business objectives or technologies.
- Integrate FinOps Practices: Provide development teams with dashboards and tools to visualize the cost implications of their services. Fostering cost ownership at the team level is critical.
- Automate Compliance Reporting: Configure security and configuration management tools to automatically generate evidence required for audits. This transforms a manual, weeks-long process into an automated report.
At this stage, governance becomes a strategic enabler that increases velocity by reducing risk and uncertainty.
How to Evaluate Cloud Consulting Partners for Governance
Selecting the right partner to help build your cloud governance framework is a critical decision. An incorrect choice can result in a rigid, over-engineered system that hinders development, or a weak framework that fails during an audit. The goal is to find a strategic partner who understands that governance should enable, not restrict, business agility.
This requires evaluating a partner’s technical expertise, their implementation methodology, and their commitment to knowledge transfer. The ultimate measure of success is the self-sufficiency of your internal team in managing and evolving the framework post-engagement.
Key Questions for Your RFP
Your evaluation process must cut through marketing claims to assess hands-on expertise.
Here is a sample vendor evaluation checklist from our platform, showing key criteria for assessing cloud consulting firms. A robust evaluation framework focuses on practical capabilities—such as experience with policy-as-code and a clear plan for knowledge transfer—not just a list of certifications.
Incorporate these critical questions into your evaluation:
- Methodology and Tooling: “Describe your methodology for implementing policy-as-code. Do you primarily use open-source tools like Open Policy Agent, or do you favor proprietary solutions? What is the technical justification for your choice for a client with our requirements?”
- Knowledge Transfer: “Define your process for ‘enablement.’ How do you ensure our internal team can confidently manage and evolve this framework after the engagement? Provide examples of training materials and documentation you deliver.”
- Industry Experience: “Provide a case study of a governance project for a company in a regulated industry similar to ours. Detail the specific compliance challenges and the technical solutions you implemented.”
Red Flags to Watch For
Recognizing warning signs can prevent costly mistakes.
A partner advocating a one-size-fits-all solution is a significant red flag. Effective cloud governance is tailored to an organization’s specific risk tolerance, culture, and technical maturity—not based on a generic template.
Be cautious of partners who:
- Push Proprietary Tools Unnecessarily: If a consultant cannot provide a clear technical justification for why their proprietary tool is superior to a well-supported open-source or native cloud service, their motivation may be vendor lock-in.
- Lack Experience in Regulated Sectors: Governance in financial services or healthcare has specific, stringent requirements. A partner without deep, demonstrable experience in frameworks like HIPAA or PCI DSS represents a significant risk. For more on this, see our guide on building a third-party risk management framework.
- Cannot Provide Verifiable References: Insist on speaking directly with previous clients of similar size and complexity. A reluctance to provide such references is a major indicator of potential issues.
Common Cloud Governance Questions, Answered
Practical questions often arise when implementing a cloud governance framework. Here are answers to the most common ones.
How Do You Balance Governance with Developer Agility?
This is a false dichotomy. The objective is not to restrict developers but to create “freedom within a framework.” This is achieved by embedding automated guardrails directly into the development workflow, a practice known as “shifting governance left.”
Instead of manual review gates, use policy-as-code tools like Terraform Sentinel or Open Policy Agent (OPA). These tools automatically scan IaC against defined policies before deployment. Developers receive immediate feedback in their CI/CD pipeline, allowing them to remediate issues autonomously. This model increases velocity because of governance, not in spite of it.
What Are the First Three Controls a Startup Should Implement?
A startup requires maximum impact with minimum friction. Focus on three practical controls that address the most significant early-stage risks: cost overruns, account compromise, and basic security vulnerabilities.
- Mandatory Tagging for Cost Allocation: Implement a policy that programmatically blocks the creation of major compute and database resources unless they have
ownerandprojecttags. This establishes financial accountability from day one. - Enforce Multi-Factor Authentication (MFA): Make MFA non-negotiable for all IAM users with console access, particularly administrative roles. This is the single most effective control against credential compromise.
- Block Public RDP/SSH Access: Deploy a preventative control that denies any security group rule allowing RDP or SSH access from
0.0.0.0/0. This closes a common and high-risk attack vector.
How Do We Adapt Our Governance Framework for Multi-Cloud?
A multi-cloud governance framework requires abstracting policies from provider-specific implementations. The core principles—cost control, data security, identity management—remain constant. The tooling must function as a unified control plane.
Your governance framework acts as a universal translator. It defines the “what” (your single source of truth for policy), then uses the native enforcement mechanisms of each cloud—like AWS Service Control Policies, Azure Policy, and GCP Organization Policies—to handle the “how.”
This means a policy like “prevent public data storage” is defined once. Automation then translates this rule into an S3 Block Public Access configuration in AWS, an equivalent enforcement on Azure Blob Storage, and the corresponding control on Google Cloud Storage. The intent is centralized; the implementation is cloud-native.
Finding the right expertise is crucial for building a framework that works for your unique environment. At CloudConsultingFirms.com, we provide data-driven comparisons of top-tier cloud partners to help you select the firm with the proven experience to guide your governance strategy. Explore our independent reviews at https://cloudconsultingfirms.com.
Peter Korpak
Chief Analyst & Founder
Data-driven market researcher with 10+ years helping software agencies and IT organizations make evidence-based decisions. Former market research analyst at Aviva Investors and Credit Suisse. Analyzed 200+ verified cloud projects (migrations, implementations, optimizations) to build Cloud Intel.
Connect on LinkedInContinue Reading
Insights
Explore our complete insights hub
AWS vs Azure vs GCP: A Strategic Comparison
Explore our strategic comparison of AWS vs Azure vs GCP. This guide provides actionable insights for choosing the right cloud platform for your business needs.
The 12 Best Multi Cloud Management Platforms for 2026 and Beyond
Discover the best multi cloud management platforms for 2026. Get an actionable, no-fluff comparison of features, pricing, and use cases.
Stay ahead of cloud consulting
Quarterly rankings, pricing benchmarks, and new research — delivered to your inbox.
No spam. Unsubscribe anytime.